Here at Opinsys we've been busy trying to figure out how to make user management work easily without having to use ugly tricks to glue different applications together. Changing password sounds really simple to many, but it often gets quite complicated as there are many passwords that need to be changed. It is possible to write a script to change the different passwords at the same time, but that limits password changing to that single script. Using GUI programs through PAM or Moodle to change the password require a different approach.
In earlier posting I went through the setup for using SASL to get rid of one password, but that left us still with Samba passwords to be changed separately. As one commenter noted, there has been for a long time an OpenLDAP overlay called smbk5pwd that syncs Heimdal kerberos and Samba passwords automatically when the password is changed in OpenLDAP. It works by intercepting the ldap exop password change operations and doing its own magic. We've been using MIT Kerberos until now and as it is the better maintained kerberos implementation in Ubuntu, we wanted to keep using it.
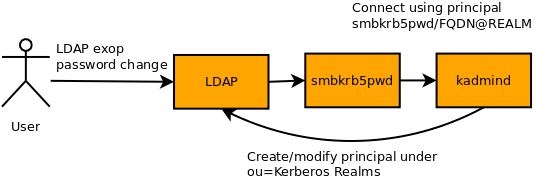
As there was no existing solution like smbk5pwd for it, we decided to implement one. smbk5pwd modifies the kerberos keys directly in the database, but we were not brave enough to try the same with MIT Kerberos and instead chose to use kadmind to create the principals in ldap. This approach uses extra network connections and it is possible that changing password fails because connecting kadmind fails or kadmind cannot connect back to ldap. Having a system where ldap server connects to kerberos server that connects back to ldap is not an optimal solution, but so far we haven't seen problems arising from this. On the other hand not having to deal with kerberos internals is a definite plus.
If you are brave enough, here are quick instructions on how to use the overlay. This is now the first version of the overlay and it has not been in production use anywhere. It's still missing features and ACLs need to be checked out, so this is work in progress.
Installation instructions
The source code for smbkrb5pwd overlay is available here.To compile the overlay the easiest way is to get the full source code for OpenLDAP and place the smbkrb5pwd directory under contrib/slapd-modules directory. After compiling OpenLDAP normally the overlay can be compiled simply by:
cd contrib/slapd-modules
make
sudo cp .libs/* /usr/lib/ldap/
A precompiled version of smbkrb5pwd for Ubuntu 10.04 (Lucid Lynx) is available from Opinsys PPA in Launchpad:
sudo apt-get install slapd-smbkrb5pwd
dn: cn=module{0},cn=config
objectClass: olcModuleList
cn: module
olcModulepath: /usr/lib/ldap
olcModuleload: {0}back_hdb
olcModuleload: {1}smbkrb5pwd
dn: olcOverlay={0}smbkrb5pwd
objectClass: olcOverlayConfig
objectClass: olcSmbKrb5PwdConfig
olcOverlay: {0}smbkrb5pwd
olcSmbKrb5PwdEnable: samba
olcSmbKrb5PwdEnable: krb5
olcSmbKrb5PwdMustChange: 2592012
olcSmbKrb5PwdKrb5Realm: EDU.EXAMPLE.ORG
olcSmbKrb5PwdRequiredClass: posixAccount
| Attribute | Possible values | Description |
| olcSmbKrb5PwdEnable | samba / krb5 | Enable samba/kerberos functionality of the module, same as olcSmbK5PwdEnable in smbk5pwd. If attribute is not set or both are set, both passwords are changed. |
| olcSmbKrb5PwdMustChange | e.g. 31536000 (year), 2592000 (30 seconds) | Time in seconds before the password expires (currently affects only Samba) |
| olcSmbKrb5PwdKrb5Realm | e.g. EDU.EXAMPLE.ORG | Kerberos realm used to create user principals |
| olcSmbKrb5PwdRequiredClass | e.g. posixAccount | If set, the entry needs to have this object class for the kerberos principal and samba passwords to be modified |
10.11.12.13 server.edu.example.org server
sudo kadmin.local -q "addprinc -randkey smbkrb5pwd/server.edu.example.org@EDU.EXAMPLE.ORG"
sudo kadmin.local -q "ktadd -e des-cbc-crc:normal -k /etc/ldap/slapd.d/openldap-krb5.keytab \
smbkrb5pwd/server.edu.example.org@EDU.EXAMPLE.ORG"sudo chown openldap.openldap /etc/ldap/slapd.d/openldap-krb5.keytab The overlay activates itself when an password change exop request is made. This can be done for example with ldappasswd command:
ldappasswd -x -D uid=admin,ou=people,dc=edu,dc=example,dc=org -W \ uid=user1,ou=people,dc=edu,dc=example,dc=org
Happy hacking!
Veli-Matti Lintu
